One of the things that make the internet so amazing is the freedom it provides. You can be anyone, anywhere, and do anything. But, the fact that there is a screen between you and the rest of the internet doesn’t mean that you don’t need to think about internet safety.
Cybersecurity and internet safety is becoming increasingly important, not only as to protect our personal information and private data, but also the personal safety and well-being of ourselves and our children. Additionally, there is a lot to be said about mental hygiene and anxiety that is unaffected by the distance between users.
On one side, there is a set of tools that you should be using to make your devices anonymous and untraceable. On the other, there is a set of rules that you ought to follow as to prevent any issues in the old fashion way, via mob rule.
In all cases, staying anonymous is the best policy. You should use a premium VPN provider such as Le VPN to protect you from hackers, snoopers, and malicious software, and you should use some tested tricks to protect you from more human dangers that lurk on the internet.
Safety Rules vs. Internet Laws
Three terms should not be confused with each other: Internet Safety Rules, Internet Laws, and Internet Regulation.
Internet regulation is what governments and international bodies make to secure their citizens from the dangers that they may face while online. In some cases, these laws are good and very beneficial to you as a user.
But, there are many occasions where laws were made by people who either do not understand the internet or have some ulterior motives. Regardless, internet regulation is something that should be used, but not necessarily followed at all times.
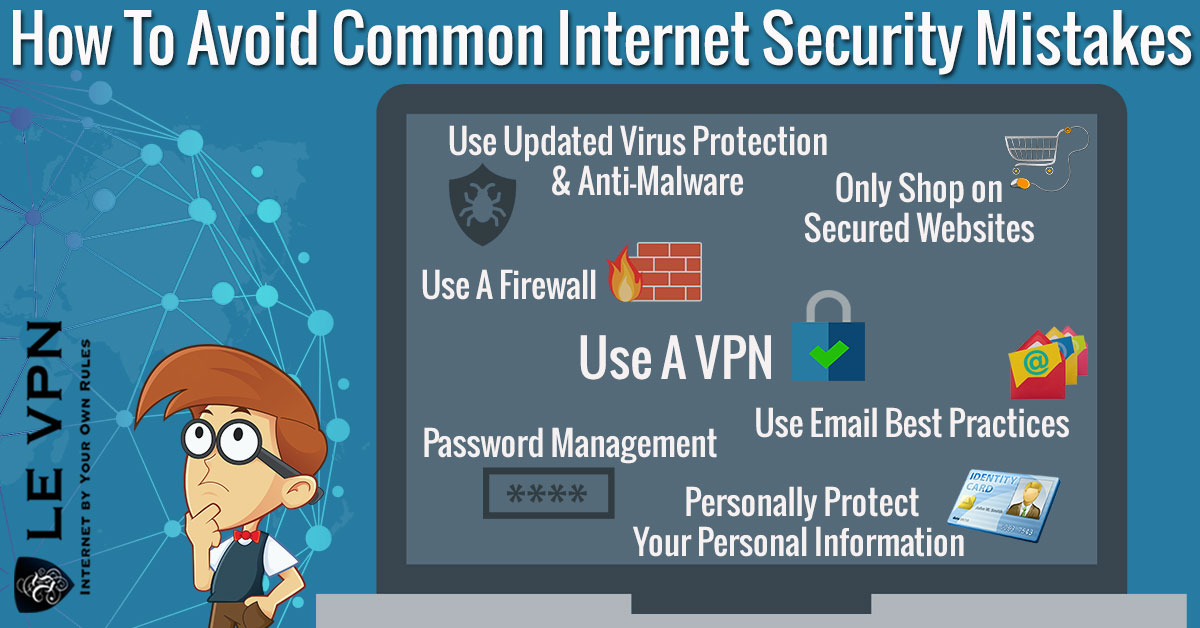
Internet safety rules are tips, tricks, and advice about what you can do to protect yourself on the internet. They usually include common sense when using the internet, as well as some tried and tested techniques. Anything from using a Virtual Private Network (VPN) to having an updated anti-virus and anti-spyware software falls into this category.
Finally, Internet Laws are a set of humorous and semi-humorous rules that reference internet etiquette. These laws include something like Godwin’s Law that states that you can’t call people ‘’Hitler” in online communication or Po’s Law that says that some people online will have views so ludicrous that you will not know if they are joking or not.
These ‘’laws” are good to know but don’t actually influence your cybersecurity.
Using Common Sense
Your biggest and strongest weapon when ensuring your internet safety is your common sense. If you feel like something is wrong, it is because it usually is. A balanced, calm approach will save you almost every time. While there is no such thing as common sense educations, calmly doing your best is usually everything it takes.
Additionally, there is some advice that has jumped the divide between the physical world and the digital. This includes calm and composed behavior and not responding to provocation.
Many people think that these internet safety rules are made by removing violence from the equation, but that is very far from the truth. While there is no physical violence online, emotional and mental abuse can often make even deeper scars than cuts and bruises.
Do Unto Others As You Would Have Them Do Unto You
This is a fundamental rule, but many people don’t follow it because they think that it has nothing to do with internet safety. In reality, molesting others and acting poorly will come back to bite you as more and more people will band together to kick you out from any support systems that you might have access to.
Additionally, if you have any personal information posted online you are exposing yourself to online vigilantes that will try to dox you, or worse.
Sounding Too Good to Be True
If you have been on the internet long enough, you have probably been informed that you are a winner of some unknown lottery or are entitled to a reward as a millionth customer. As you probably know, this is a lie.
Scammers have used this trick since the early days of the internet to trick gullible or greedy people into sharing their private information or even sending money. Once they have the info, they just disappear and usually sell your data to many other people.
The tricks being used now are less evident than before and usually focus on some piece of information that they have, like your IP address. Thankfully, if you are using a VPN provider like Le VPN that has servers in other countries you will be immune as the few scams coming your way will be in different languages and reference places that you are not familiar with.
Stay Anonymous
This should be the first rule of the internet. Staying anonymous doesn’t only mean using a VPN with a secure anonymous proxy server so that people can’t see your IP address, but not sharing your real name either.
Online anonymity ensures that we can use everything that the internet has to offer without putting our mental health or physical security at risk.
The first benefit of anonymity is that nobody will know how to hack you, steal your personal information or make an attempt on your bank account. Nobody can steal your identity if there is nothing online to take.
The second benefit is that you will not endure harassment due to your identity. Your race, sex, gender, religion, ethnicity, or political affiliation doesn’t even matter to online harassers; somebody will find it appropriate to attack you because of them. But, if the person on the other side doesn’t know who you are it is impossible to hurt you emotionally in any significant way.
Data Dissemination
If we were to take a closer look at our habits, we would be amazed at the amount of personal data that we give every day. At that moment it doesn’t look too dangerous to give that teller your name, address, and phone number, but that can lead to your entire identity getting stolen by an identity theft scheme.
This needs to change. We need to be more mindful about who we share our identity with and who can have our information. You will probably not win that lucky draw between over a million Target shoppers, and you can probably find out about the new offers without being subscribed to the newsletter.
Finally, it is possible to have a ‘’persona’’ that will act like an IRL VPN. If you really like collecting coupons and entering online games, give a pseudonym that is connected to an email address that is under that same name, as well as a burner mobile phone. While it does sound a bit ‘’cloak and dagger’’, it can even be fun, and will not endanger your actual identity.
TMI
Proof that people love oversharing their life online is that there are even apps like Twitter that are used almost solely for this purpose.
Not only is TMI (Too Much Information) unsightly and vulgar, it can also put you in a lot of trouble. From stalkers that can use that information to harass you in real life to data thieves that will use everything you say against you.
Lotteries, Winners & Losers
Not every online lottery is a scam, but giveaways and similar exhibitions are infamous for their lax attitude about personal info that they collect.
This doesn’t just include famous individuals giving away some branded merchandise, but also large companies that offer coupons and other benefits for people who give them their private information. Not only are these companies often the target of hacking, but it is also possible that there is someone on the inside that is corrupt and selling your information to the highest bidder.
As we mentioned before, you may try with a fake persona, but never give out your real information.
Joining the Mailing List
Similar to the last point, you might be offered to join a mailing list from all kinds of entities. In these cases, it is vital if you are giving some information beside your email. Information requested can be your name, your house address, or even your credit card number.
If you are using a good email service, and you have a VPN, you can give only your email address. But never give out your name or any other information. If you have a work email, you can use that one, as it is not connected to other data, but that is only if you trust in the cybersecurity of the company you work for.
Talking to Strangers
Apparently, mama knew all along. The fact that you are an adult doesn’t mean that you should stop listening to what your parents said and talk to strangers.
Giving out any private information to someone calling you and presenting themselves as ‘’customer support” is nothing but dangerous. If they are indeed the person they say, they would already have all of the information they need on file. If they don’t have it, they don’t need it.
Additionally, no representative of any company will ever ask you for your username and password for that company, as they don’t have access to that information regardless. Also, information such as your social security number or credit card number will never be asked for over the phone.
If someone asks you for that information, write down the phone number or email and make a complaint to the company that they mentioned, as it might be compromised.
Finally, this includes giving your data to ‘’free internet’’ providers, such as when you are at a café. That fake email might come in handy here, as well as a good VPN hotspot app.
Social Media Etiquette
This is quite a new field when it comes to internet security and one that is still not entirely understood. Internet use for social media is expanding, and so are the threats.
From everything, we do know, social media shouldn’t be understood as merely talking to your friends, but more as shouting to your friend in a bustling market. While most people won’t care what you have to say, you may garner some unwanted attention.
This attention can be from three distinct groups: government, criminals, and the mob.
While having trouble with criminals, scammers, thieves, or bullies is something most people are afraid of, it is not the most common type of attack. When you are not anonymous when using social media, you will often become a target of cyberbullying and harassment, for a whole range of issues.
It is not important what sort of event, idea, or any other thing you have, someone will be there to annoy or harass you over it. Black, white, left, right, rich, poor, gay, straight; someone has a problem with that on the internet.
What’s really in Your Pictures?
Facebook and Instagram users can often be tempted to share a lot of pictures of themselves and their family on social media.
If you are very careful about your account security and who you can see these pictures you might be okay, but you should always check what can be seen in your photos. Some of these images are even geotagged and will show your exact location, while others can have your street name or even exact home address on them.
This can attract stalkers and data thieves alike, and can be a whole lot of trouble for not as many ‘’likes’’.
If you really like that selfie in front of your new home, at least make sure to blur-out the address and disable any location services.
Online Bragging
It can be tempting to show off to your friend and colleagues about the new car you got, or about your promotion, but that is probably something that you should show in person and not online.
On one side you will provoke some unwanted bile from people who are jealous about what you earned, but that will not create as many problems. What will create a problem is that you are exposing the fact that you have something to the people whose job is to steal something.
Data theft is quite tempting when the hackers know the person has good credit and a good job.
Exposing Others
Finally, you might not think a lot about it today, but you should avoid doxing your children and loved ones. Hackers might not care about your baby photos now, but it will be a good thread to pull once they are older.
Additionally, even if it never creates a problem, it will be embarrassing at some point, and you should leave your child to embarrass themselves on their own accord.
Online Safety for Children
Internet safety tips for kids vary greatly depending on their age and level of exposure. A good way to measure that level as a parent is to assert the level of exposure you think they have and then double it.
While there is a lot that has been done to promote internet safety for children, including numerous campaigns as well as the Children’s Online Privacy Protection Act (COPPA), nobody can take care of your children if you yourself don’t follow internet safety 101, which can be safely abbreviated to ‘’be anonymous on the internet’’.
Chatroom Self-Defense
Martial arts are a good thing to know in school, as bullies are not willing to attack you if the outcome of that attack is unknown. Also, it gives you confidence and some emotional stability.
But, unlike the school courtyard where you can tell when someone’s being bullied, chat rooms are away from the public eye, and a cyberbully can be anyone, regardless of their size and age.
That is why you should teach your child how to argue. Teach them to be calm and composed, and not to take things to heart. Sticks and stones. Play a game with your kid where you come up with comebacks and give them advice on how to be quick on their feet.
This will not only train them to survive online interactions when social networking in the future, but will also improve their social skills and personal relationships.
Trust Your Children
Don’t brush off if your child says that they are being harassed or bullied. It is not ‘’just the internet’’ as it can often be quite emotionally painful. Bullying and cyberbullying are serious issues.
Show your kids that you understand and devise a strategy together how to fight against the issue. Don’t overreact and don’t try to fight your child’s battles instead of them, help them fight their own battles and show them how calm heads always prevail.
Report Cyberbullying
The fact that you didn’t overreact in front of your child and started calling the school, threatening lawsuits, doesn’t mean that you shouldn’t report cyberbullying. Child safety is something most institutions value quite highly, and is not something to be negligent about.
Call the school, and the police, and make an official report that your child is being harassed. In many cases, the bully is also going through emotional and domestic issues, and you might save more lives than one by speaking up.
Make a Clone Device
Finally, while you might trust your child to tell you everything that they are doing, make a clone of their device as to see their chats and correspondence.
Never, ever, publicly act on this information. Just modulate your approach.
Also, at some point you will want to destroy that device, usually around the age of 15. You know what you talked about when you were that age. It is not something tender parental eyes should see.
Use Tools at Your Disposal
To have the best experience on the internet, you would be wise to use all of the tools at your disposal. From the most basic behavioral adjustments to the most technical solutions, everything should be used as much as possible.
On your devices, be anonymous, use a VPN, have good anti-virus software and stay away from any software you don’t trust. On the family front, train both your loved ones and yourself how to be resilient and vigilant. That way you will see any issues quickly and resolve them even faster with very little damage to your psyche.
Finally, don’t be afraid to call the authorities, including law enforcement. Cyberbullying, harassment, and especially hacking are getting the recognition they deserve as being very destructive for people’s lives. Don’t be silent about them.
Conclusion
The main thing everyone should understand about online threats and cybersecurity is that you are not defending your devices, but rather yourself. While premium VPN providers like Le VPN can make your devices become anonymous during your internet activities, making them secure against hackers and snoopers, you still need to protect your privacy like you would in real life.
Practice cyber hygiene, be private and teach your kids and loved ones to do the same. The best way to use the internet to its full potential is to be smart, be vigilant, and stay safe as much as possible.
EXCLUSIVE DEAL
First 3 years for $2.22/mo