It is a time long past when most people were not concerned with cybersecurity and internet security in general, as now the average person has most of their lives stored on some device or other. What had, regrettably, survived to some degree is the notion that because you think that you don’t have anything of real importance on your private devices you would not be a victim of malicious entities on the internet. While you see your cute selfies as just something you do when you are bored, hackers see those as another identity that they can use to scam people online, using your face.
Aside from your identity, there are other things most malicious entities online would find enticing. Your browser history, your IP address, your processing power, your clearance for your company or other institutions; all of this is something that different people can use to make illegitimate gains in one way or the other.
The Cost of Cybersecurity
While keeping your identity, property, and information is not free of charge, it does not require that many funds, especially when you take into account the importance of what they are protecting. While some people house a large variety of important data in multiple devices and should opt for an elaborate security system that will protect all of their devices and communications, most people can find sufficient security using a well-made and well protected Virtual Private Network (VPN) that they would be able to install on all of their devices.
To ensure cyber safety, you would need to delegate a little bit of time to research and install all of the needed software, and on occasions hardware, and a little bit of money to maintain and update all of your systems from time to time.
Research
There are two aspects that you will need to understand if you would like to fight cybercrime and cybercriminals that want to take your precious data. First of all, you would need to assess your own needs and devices that you use every day. If your only connection to the internet is your laptop, then your job is easy as you only need a good VPN and a good Anti-Virus and you are set to go. Some VPN providers, like Le VPN, will offer you VPN connections for multiple devices and for multiple platforms, which would be the easy choice if you don’t want to spend a lot of time on assessment and maintenance, as the provider would do that for you.
Installation
While this used to be the biggest problem for most people, installing cybersecurity software now is fairly easy for everyone. You will just need a couple of clicks to install any Anti-Virus or VPN software, which usually functions over an app specially designed for the platform you are using.
Depending on the number of devices you have, making your whole life secure might take some time, but even for the neediest of people, this wouldn’t surpass a few hours, at most. This should be done as soon as you acquire the device, as to reduce the time you are exposing yourself to risk.
Upkeep
There are two things you will need to maintain as to ensure your cyber safety: operating systems and security systems. Cyber attacks usually exploit loopholes and deficiencies in the operating system, and that is the reason why patches and updates for these systems come out so regularly. Developers and coders in Microsoft, Apple, and similar OS producers have a goal of always staying ahead of the curve and dealing with issues before they impact many, if any, customers.
In the same way, reputable VPN providers will ensure that your cyber protection is always up to date and it is up to you to check for updates regularly.
The Cost of not being Cyber Secure
What is cybersecurity? How does it affect our private lives? The worst way to find out is not to be secure. There are multiple factions that are after your data and personal information, and all of them plan to use your information to either strengthen their existing hold over your life or illegally benefit without your consent.
While cases, where cybercriminals will endanger your physical body, are rare, all other aspects of your life are at stake. Your name, your savings, your property, and your reputation are at stake as both hackers and companies vie to use them either to target you with sales and offers that would exploit your sensibilities or to just take your identity by force. Even if you don’t have much money in the bank, a loan could be taken in your name, or your credibility as an honest person can be used to trick other people, and losing face is often even worse than losing money.
Personal Information Leak
One of the primary things most malicious entities on the internet are after is your personal information. The history of cybercrime starts and ends with governments, corporations, and hackers trying to obtain your name, social security number, credit card info and other information that can be either used as means for an identity theft or some other malicious ruse.
In most cases, the hackers will exploit vulnerabilities in either your system as a whole or in your approach to dealing with cybersecurity threats, or the lack of such, waiting for the opportune moment to use your information and potentially ruin your life.
Personal Data Theft
The data that you store inside your devices should be viewed as a separate target than your personal information, mainly as hackers and other entities don’t need to know who you are to misuse your data. There are two types of things hackers are looking for when they gain the ability to take your data.
The first thing is ransomware which may either be some intellectual property that you haven’t published yet or some type of private data such are personal images or videos. This data can be used to request ransom from you if you don’t want those items to be published as a result of a ransomware attack.
The second thing is ‘’Catfish Food”, which mainly focuses on your images and affects predominantly young women. Your images might be taken and used on different websites, usually dating websites, as to scam other users to send money or their personal information.
Professional Information & Data Leak
If you work at a prominent company and have high clearance, it is probable that you have some sort of professional information on your personal computer or other devices. This information is a target for both hackers and more malicious companies that would like to have some easy access to cyber espionage. Here is where a good VPN is of great service, as the data you have is usually partial, and if the hackers are unable to target you directly you would be impossible to trace.
Backdoor to Your Devices
To quote Windows before you register, ‘’you might be a victim of software counterfeiting’’. It is possible that you already have malicious software or some hackers have already gained access to your devices and are just waiting for an opportune moment to attack. Most serious cyber security breaches in companies were made by using devices from unaware employees that are just laying in wait to jump from your personal device to your professional working station. This may have serious repercussions as it is very hard to prove that you are not the one hacking your place of employment, and in most countries this sort of behavior is a serious crime that will cost you a lot of time and money in legal fees, not to mention that it will probably cost you your job.
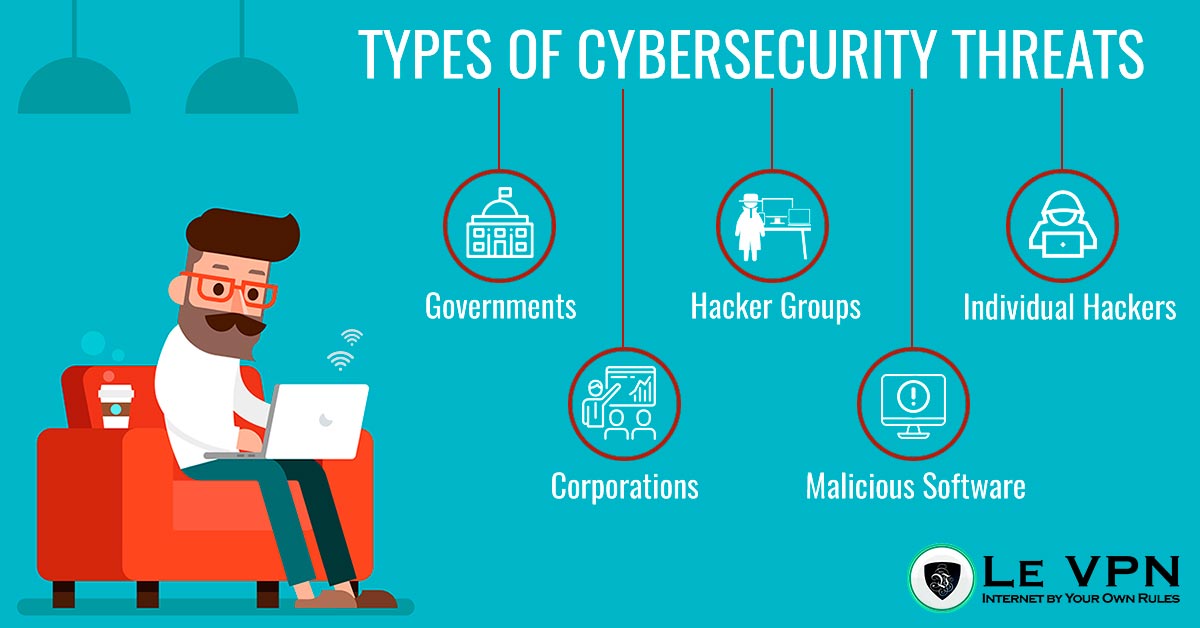
Recognizing Threats: Types of Cybersecurity Threats
It is very important to recognize the type of threats you yourself are exposed to as personal and individual cyber security threats differ greatly from small business cyber security threats both in persons being the main culprit of the possible cyber-attack and the information they might be after.
For individuals, it largely depends on where they live, what sort of platforms they use, and if they take care of their behavior on the internet. While anonymity is a good solution to most problems, it is not always possible to keep all of your personal information off the internet, much because future employers would be suspicious about people who have no trace, and in the modern age it is quite hard maintaining a social life without any social media.
Governments
Although most people imagine some authoritarian regimes as prime culprits in misusing and stealing your information, the recent scandals with Homeland Security and the National Security Agency (NSA) have proven that even democratic governments such as the USA are not beyond collecting their citizen’s data as a means to enforce security and stability. More authoritarian countries have even worse reasons to obtain your information, as in some parts of the world it is illegal to say or do anything that can be viewed as anti-government or against some obscure religious norms.
Finally, some states will fine you if you are enjoying media and content that the government has deemed to be ‘’improper’’, even if it is not in the slightest political. The United Kingdom and Australia are just some of these countries.
Corporations
Corporations are the primary nemesis of privacy, as their wish to either sell you some of their products and services or to sell your information to other corporations to do the same surpasses any notions of law or even decency.
Top 10 biggest data breaches of all time are all due to major corporations collecting and mistreating information obtained from their customers, and in many occasions, it has been proven that they even had information from people who were not their customers, but which they have bought from other sources.
Hacker Groups
To be fair, most hacker groups are totally uninterested in personal information and are only focused on fighting the previously mentioned governments and corporations. That being said, there are some groups that work similarly to a regular crime organization, using identity theft, extortion, and other methods to line their own pockets with other people’s money.
The only good thing about these organizations is that once they gain prominence they usually get either arrested or employed by said corporations to make cybersecurity systems. This means that if your OS and VPN are up to date, you will definitely be ahead of almost all hacker groups.
Individual Hackers
This is the most problematic type of hackers as there are as many reasons why someone would steal any information as there are individual hackers. These persons usually use cyberstalking over social media and other methods and they usually fixate on specific targets.
While having a good cyber security system will almost always give you a technological advantage to individual hackers, be advised that these persons can use physiological tactics to gain access to your system and are not beyond even using cyberbullying to bate you into giving your personal information. Use skepticism, and stay vigilant.
Malicious Software
Most people think that malicious software is something only found on adult websites and other dark corners of the internet, while actually, the opposite is true. Malicious software is made to endanger the easiest of targets, and people going to the dark web are usually very mindful of their cybersecurity. The biggest disseminators of malicious software are social media sites, as most users of those sites don’t take enough care of their protection online.
Different Solutions for Different Situations
As always, there are different solutions depending on your type of activities on the internet and the devices you use for that purpose. An updated Operating System, a good Anti-Virus, and a reputable VPN will shield you from most troubles, and if you know exactly what you are using you will always be safe while browsing and buying on the internet.
VPN Security
A Virtual Private Network, or VPN, is the best way to shield yourself from most problems you may encounter online. The primary role of a VPN is to hide your IP address, making it impossible for malicious entities to target you directly and more advanced VPN providers offer a wide range of services that make your stay online easier and safer.
IoT Security
If you opt for a secure VPN, like Le VPN, you will have the option to secure multiple devices in your home from the same account, including your laptop, mobile devices, and probably even your self-driving cars in the future. Nowadays there are smart devices everywhere, from your printer and other peripherals, and even your refrigerator and AC are connected to the internet. Using a good VPN app and forwarding all of those devices through that connection will make it almost impossible for entities without clearance to access your home devices.
Advantages of Using a VPN
There are multiple advantages when using a VPN, and not all of them are connected to cybersecurity. There is a major advantage in using VPNs when enjoying your civil liberties, such as watching a good movie that is, for some reason, denied by the government.
There are three aspects of cyber protection where VPN shines as a good example of security practices: Anonymity, Targeting, and Data Usage. Denying malicious persons the ability to attack some key points in your security will make it impossible to all but the top hackers from obtaining your information, and to be at risk from them you would probably have enough means to hire a professional cybersecurity team.
Anonymity
This is the primary service of a VPN. By concealing your IP address the VPN provider makes you anonymous to online software that is monitoring your actions. This will not only protect you from hackers and identity thieves but will also shield you from a targeted advertisement from corporations and companies, as well as their ability to sell your browsing history to their partners.
Hard Target
If you are both anonymous and secured internally, you will become both a hard target to breach and a hard target to hit. This fact alone will prove enough to most hackers not to even attempt to hack your devices.
Modern hackers have ways to assess what kind of protection you have, usually comparing your behavior to the data provided by the IP address you use. If, for example, you live in China and your IP address is listed in Singapore, the hackers and other entities will know that you are using some kind of protection and would probably not risk exposure.
Trying to hack a reputable VPN provider would prove almost impossible, as companies like Le VPN are employing expert developers that make sure that all traffic through their servers is safe and secure.
Unusable Data
Finally, even for those individual hackers that may acquire some information from non-internet means, having partial data such is only your name, or only your home address will prove to be useless when trying to harm you. Without having your actual IP address, in combination with all of your personal information, it is impossible to steal your identity as the IP provided by the VPN provider can’t be cloned.
*Article Updated On February 5th, 2019.*
EXCLUSIVE DEAL
First 3 years for $2.22/mo




Written by Vuk Mujović @VukMujovic
Vuk Mujović is the founder of MacTíre Consulting, an analyst, data management expert, and a long-term writer on all things business & tech. He authored blogs, articles, and opinion pieces aimed to help both companies and individuals achieve growth without compromising their security. Vuk is a regular guest author to Le VPN Blog since January 2018, where he gives his expert opinion on the topics related to cybersecurity, privacy, online freedom, and personal data protection. He also often shares his tips and best practices in relation to internet security and digital safety of private individuals and small businesses, including some additional applications of using a VPN service.
Comments (1)
I think it’s an issue that companies like Google can collect tons of information about us completely legally. We would be really uncomfortable if we found out that a person had access to that information.
I think there is a problem with culture on the internet that says it’s okay for companies to collect as much data as the do.